Methods of cloud data protection
In addition to the best practices listed above, cloud data protection can be well-served with these methods.
Automate the cloud
Downscaling the amount of human interaction from the resources within the cloud via automation can help protect data in the cloud. This helps with both threat and anomaly detection, as well as in the response. When automation is built into the cloud infrastructure, changes and updates can be launched and completed in seconds rather than days, weeks or months.
For example, AWS can interact with APIs and send a single command line to kick off a series of scripts that launch the relevant instances and containers needed for the entire cloud environment. In addition to time efficiency, cloud automation also eliminates human error and cloud misconfiguration.
Partner with a third-party cybersecurity risk management team
Vet and employ an independent, neutral tool that analyzes and reports on your organization’s security preparedness. BitSight, for example, helps monitor an entity’s public footprint online.
Both cloud providers and the enterprises leveraging a cloud provider’s services can benefit from these third-party assessment tools. The feedback can be used both proactively and reactively:
- Proactive monitoring: Validates that the things your cloud security team is doing internally are not reflecting differently on the outside.
- Reactive monitoring: Validates that your cloud security team is doing what they’ve said they are.
Top-tier cloud service providers will use these third-party assessors to monitor their scores as well those of customers, vendors and payment processors.
Infrastructure as code (IaC)
By managing and deploying your cloud infrastructure as code rather than through manual processes, you limit human error and the intrusion of bad actors — both internal and external. IaC forces your cloud administration through the same security lifecycle development process that application coding would go through to assure it’s not malicious.
Cloud data security issues and challenges
Cloud infrastructure speeds business and enables organizations to work in real time, anywhere. It drives cost savings, frees up physical space, supports the modern, remote ways we work, and supports disaster recovery preparedness.
However, cloud computing does face issues and challenges, including:
Access control
Knowing who can access what data is in your cloud environment is important for data security. Cloud service customers should know who’s validating access and require strong precautions around data-level access and crypto keys, as well as ensure their cloud service providers follow the best practices we’ve discussed above, from culture to defense layers.
Unfortunately, poor access control visibility can let malicious actors (often insider threats) into your cloud setup.
Supply chain attacks
These attacks are orchestrated, originally, against the software of a larger organization’s smaller partner. As large enterprises have become savvier in the data protection game, malicious actors have increased their attacks on smaller vendors who may sell their product to a larger entity. Once that undetected, infected partner software is unleashed into the target enterprise’s cloud environment, it infects all users of the application.
These supply chain attacks can impact suppliers, and then the suppliers of your suppliers, creating a chain infection of malicious coding. They can also be hard to trace because of the lengthy chains.
Inventory of assets
Organizations with lackluster asset management protocols may not know what assets and data they have in the cloud. Or because the nature of today’s fast-paced cloud is that pieces are spun up and destroyed at a rapid rate, cloud security teams may not be able to keep pace with what’s happening within the environment.
To combat this vulnerability, organizations should know what’s in the cloud, why it’s there and who’s managing it. This will help for forensic analyses as well, so that if a breach does occur, your cloud security team can track ephemeral systems.
Bottom line: You can’t secure what you don’t know is there.
Cloud expertise shortages
The industry faces a cloud expertise shortage, and some of the biggest security challenges come with it. If employees without the critical cloud expertise try to deploy assets into the cloud the same way they do to their traditional datacenters, things can go quite wrong from a security perspective. While the two skill sets can complement each other, they’re not a like-for-like match.
Add in the speed of the cloud, and how quickly cloud providers can modify and replace their own services, and it’s exceptionally challenging for noncloud experts (and cloud experts) to keep up.
> Read more | The tech workers you need are nowhere, anywhere and everywhere
Cloud vs. datacenter security
The difference in security between cloud computing and on-premise datacenters is essentially who owns the liability.
An on-premise datacenter that doesn’t utilize the cloud has servers that are owned and managed by the enterprise. In that scenario, the organization is fully responsible for security.
When an enterprise partners with a cloud-enabled solution that leverages a cloud provider, the datacenter security responsibility shifts to the cloud provider.
However, the organization must do its due diligence in vetting all suppliers, vendors and providers who have any hand in the cloud infrastructure, applications used and services procured. Ideally, this means an enterprise selects a major provider, such as AWS, which would have the highest levels of cloud security talent working on them and proven track records of security success.
Will cloud replace datacenters?
No, the cloud doesn’t replace datacenters. A cloud solution still uses a datacenter for data storage. However, most enterprises are moving away from managing their own on-premise datacenters. Cloud providers own and manage their own datacenters, and they essentially “rent” storage space out to partners.
For example, AWS is a cloud provider that manages its own datacenters that are used to store their partners’ cloud data. AWS is responsible for the security and upkeep of those datacenters, and that’s where they store the data of their cloud infrastructure customers.
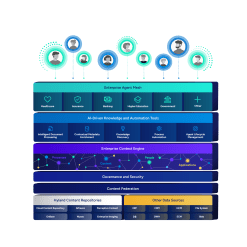
Cloud data security for content services
Hyland is a leading content services provider with a range of cloud-enabled and cloud-native technologies, solutions and services. We take cloud data security seriously because our customers demand it, and because it’s the right thing to do.
Hyland and cloud computing
Learn more about Hyland in the cloud:
Hyland on AWS
Hyland is listed on the AWS Marketplace. Learn more about the benefits of purchasing there, including the ability to:
- Streamline procurement
- Implement controls and automate provisioning
- Manage software budgets with cost transparency